Programs Don’t End
Why your compliance certification is just the beginning of the hard part — and what practitioners can actually do about it.
You passed the audit. The report came back clean. The certificate arrived — framed or digital, depending on your org’s personality. Someone sent a Slack announcement. Leadership nodded. Maybe there was even a small moment of celebration, because you and your team had worked hard and it showed.
And then Monday arrived.
The auditors went home. The consultants closed their laptops. The cross-functional working group disbanded back into their “real” jobs. And you were left holding the thing you built — the policies, the controls, the risk register, the evidence library — with a quiet, dawning realization nobody had prepared you for:
The project is over. The program has just begun.
THE MOMENT MOST COMPLIANCE EFFORTS QUIETLY FAIL
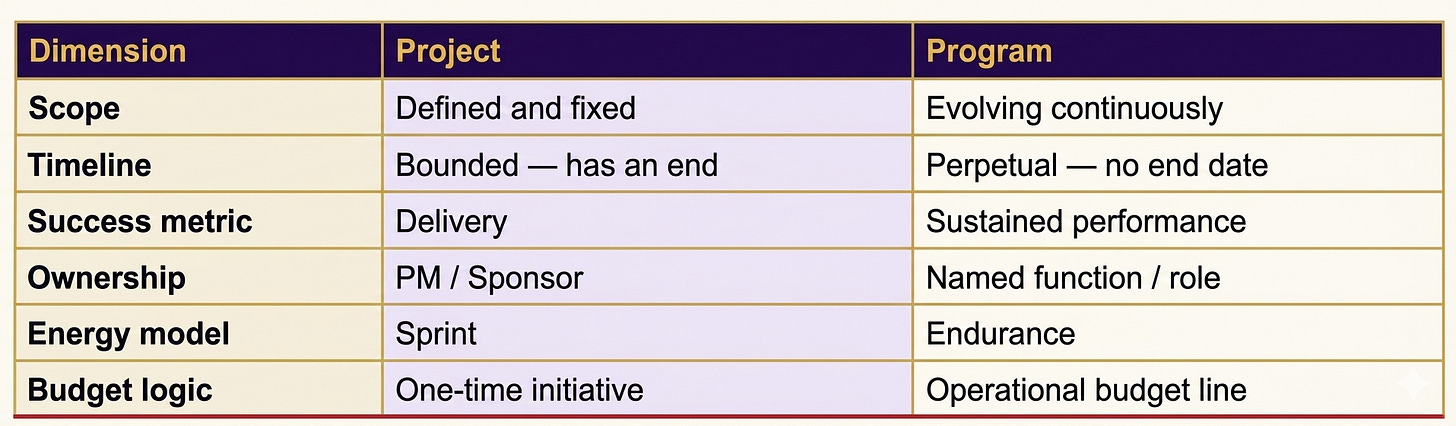
That distinction — between a project and a program — sounds academic. It isn’t. It is the single most important conceptual shift separating organizations that sustain compliance from those that fail their next audit and can’t figure out why.
The finish line that isn’t
Projects have finish lines. Defined scope, bounded timeline, a delivery event, a close-out. You build the thing, you ship the thing, you move on. Programs don’t work that way. Programs have a heartbeat — they require oxygen, ongoing attention, and energy not to launch, but simply to stay alive.
Project vs. Program
Compliance frameworks — ISO 27001, SOC 2, ISO 9001, ISO 42001, HIPAA — are designed as programs. The standards tell you this explicitly: surveillance audits, recertification cycles, management reviews, continual improvement clauses. The word “continual” appears in ISO 27001 not as aspirational language but as a structural requirement.
REAL-WORLD PATTERN
A mid-size SaaS company earned ISO 27001 certification after a nine-month sprint. Eighteen months later, during their first surveillance audit, auditors found that eight access control reviews hadn’t been conducted, three policies were never updated after a product replatform, and the risk register hadn’t been touched since certification day. They didn’t lose the certificate — but the remediation cost more in staff time than the original build.
This pattern repeats across industries. The build gets funded. The program doesn’t.
Key compliance cadence facts
Why maintenance is harder than the build
Here is something nobody tells you in pre-audit briefings: maintaining a compliance program is harder than building one. The build has momentum — executive sponsorship, urgency, shared goals, the psychological fuel of working toward something. Energy is not the problem during a certification effort. The program has none of that.
The team disperses. Post-certification, the people who helped build the control environment return to their primary functions. IT goes back to running the network. HR goes back to running HR. You are now running the program largely alone, with matrixed support and no institutional urgency.
REAL-WORLD PATTERN
A healthcare technology firm completed SOC 2 Type II using a dedicated cross-functional team over fourteen months. On completion, the PM was reassigned to a new product launch and the security engineer who owned most technical controls moved to a new company. The compliance documentation — complete, accurate, freshly audited — now lived in a SharePoint folder nobody had a recurring responsibility to maintain.
By the time the next SOC 2 period opened, the firm had to re-educate an entirely different set of people on why the controls existed and what “continuous monitoring” actually required. The second SOC 2 cost nearly as much as the first.
Scope creep is invisible until it isn’t. Your threat landscape evolves. Regulations update. New vendors enter your environment. A product pivot changes your data flows. The system you certified no longer perfectly maps to the system you’re operating — and if no one is watching that gap, it widens quietly until an auditor finds it loudly.
PRACTICAL TIP — CHANGE TRIGGER MAPPING
Build a one-page reference that maps common operational changes to required compliance actions. When a trigger fires, the response is pre-defined:
New vendor onboarded → vendor risk assessment + DPA review
New system added to production → asset register update + control applicability review
Employee departure from sensitive role → access review + knowledge transfer check
Incident declared → ISMS incident log entry + root cause analysis
Regulatory update published → policy gap assessment within 30 days
Governance atrophies. The risk register freshly reviewed for Stage 2 is now eight months stale. The ISMS committee meeting that was crisp and well-attended before the audit now struggles to make quorum. Exceptions pile up unresolved — not because anyone decided to let things slip, but because without structural cadence, governance drifts toward whoever is shouting loudest that day.
⚠ THE MOST DANGEROUS PHRASE IN COMPLIANCE
“We already did that.”
Past compliance is not present compliance. A control accurate eighteen months ago may be broken today. A policy reviewed at certification may no longer reflect how you operate. The certificate proves you built the system. It does not prove the system is still standing.
Institutional memory walks out the door. The person who designed your access control matrix leaves. The engineer who understood why a particular compensating control existed is gone. The logic that made your program coherent lives in people’s heads, not in your documentation.
PRACTICAL TIP — CONTROL RATIONALE DOCUMENTATION
Every control in your control set should have a brief “why this exists” annotation — one or two sentences explaining the risk it mitigates and the decision logic behind it. When the person who designed it leaves, their reasoning doesn’t.
This takes thirty minutes per control during the build phase. It saves hours of re-archaeology during maintenance.
What a mature program structure actually looks like
If the build was the project, the program needs its own infrastructure — designed for endurance, not velocity. Here is what that looks like in practice, not just in theory.
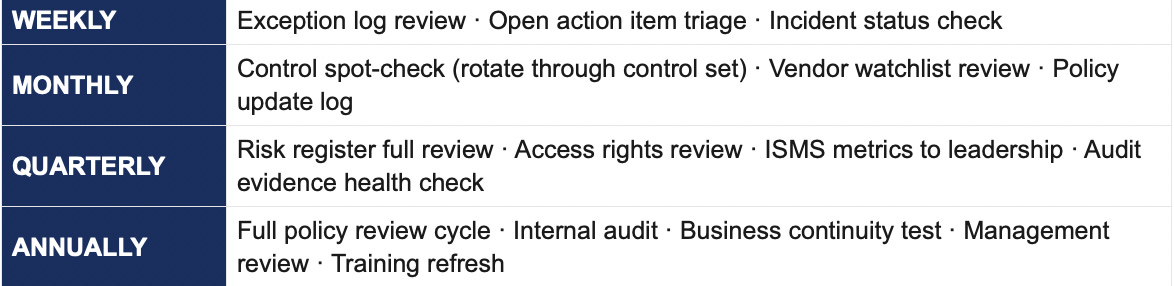
The governance cadence — a working template
The cadence is the accountability system. Without it, “ongoing” becomes “whenever we get to it” — which means never.
REAL-WORLD PATTERN
A financial services firm running ISO 27001 assigned one senior analyst as the permanent ISMS program owner — a standing function with a defined job description and KPIs. They implemented a 12-month evidence calendar: every control was mapped to a collection event owned by a named person, with a fallback owner.
When their first surveillance audit arrived, evidence collection took two days, not two weeks. The auditors noted that the program “demonstrated operational maturity beyond certification-level requirements.” That language appeared in two subsequent customer due diligence responses.
PRACTICAL TIP — THE 12-MONTH EVIDENCE CALENDAR
Map every control to a collection event. Assign it an owner, a due date, and a fallback owner. Put it in a shared calendar or your compliance platform (Thoropass, Vanta, Drata all support this natively). The goal: when an auditor asks for evidence, you retrieve it — you don’t scramble to recreate it.
You fund your finance function on an ongoing basis. You don’t hire an accountant to close the books once and send them home. Compliance deserves the same structural logic.
Getting leadership to fund a program, not a project
This is where most compliance practitioners get stuck. The certification budget was approved because there was a deliverable. How do you argue for ongoing investment when the deliverable is “we stayed compliant”?
THE BUDGET ARGUMENT THAT ACTUALLY WORKS
Don’t frame ongoing compliance as a cost. Frame it as insurance against a known, recurring event.
“We spend $X/year on the program. Our surveillance audit fee alone is $Y. If we fail a surveillance audit and need emergency remediation, the cost is historically 2–3× the original certification build. The program prevents that.” Attach a dollar figure to control drift, and the conversation changes.
PRACTICAL TIP — THE COMPLIANCE PROGRAM ONE-PAGER
Once a year, produce a single-page status report for leadership. Include:
Control health summary (% operating effectively, % with open remediation)
Audit readiness score — your honest assessment of where you’d land if audited tomorrow
Three risks actively being managed and their current status
Key program metrics: evidence collection rate, policy review completion, exception closure rate
Upcoming obligations: next surveillance audit date, policy reviews due, regulatory deadlines
This reframes compliance from “cost center with a certificate on the wall” to “function with measurable operational outputs.” It’s also the document that justifies next year’s budget in two minutes.
The leadership ask
The investment case is not complicated. Certification tells the market you built the system. Continuous operation tells auditors, customers, regulators, and partners that you kept it running. In the event of a breach, a regulatory inquiry, or a customer due diligence review, that difference becomes very material very quickly.
REAL-WORLD PATTERN
A technology services company lost a major enterprise contract during vendor due diligence — not because they weren’t certified, but because when the customer’s security team asked follow-up questions beyond the certificate, the answers revealed a program maintained in name only. Policies hadn’t been reviewed. Risk owners hadn’t been assigned. The ISMS committee hadn’t met in six months.
The certificate said they passed. The program said otherwise. The customer chose another vendor.
There is a moment in every certification journey — usually between Stage 2 and the first surveillance audit — when the organization makes a quiet, consequential decision about what kind of relationship it wants to have with its compliance obligations. It can treat certification as an event: something that happened, something to point to. Or it can treat certification as evidence: proof that it built something worth protecting — and commit to the ongoing work of protecting it.